More than 300 million children a year are victims of online sexual exploitation and abuse, according to the first global estimate of the scale of the problem published on Monday.
Researchers at the University of Edinburgh found that one in eight of the world’s children have been victims of non-consensual taking, sharing and exposure to sexual images and video in the past 12 months.
That amounts to about 302 million young people, said the university’s Childlight Global Child Safety Institute, which carried out the study.
There have been a similar number of cases of solicitation, such as unwanted sexting and requests for sexual acts by adults and other youths, according to the report.
Offences range from so-called sextortion, where predators demand money from victims to keep images private, to the abuse of AI technology to create deepfake videos and pictures.
The problem is worldwide but the research suggests the United States is a particularly high-risk area, with one in nine men there admitting to online offending against children at some point.
“Child abuse material is so prevalent that files are on average reported to watchdog and policing organisations once every second,” said Childlight chief executive Paul Stanfield.
“This is a global health pandemic that has remained hidden for far too long. It occurs in every country, it’s growing exponentially, and it requires a global response,” he added.
The report comes after UK police warned last month about criminal gangs in West Africa and Southeast Asia targeting British teenagers in sextortion scams online.
Cases — particularly against teenage boys — are soaring worldwide, according to non-governmental organisations and police.
Britain’s National Crime Agency (NCA) issued an alert to hundreds of thousands of teachers telling them to be aware of the threat their pupils might face.
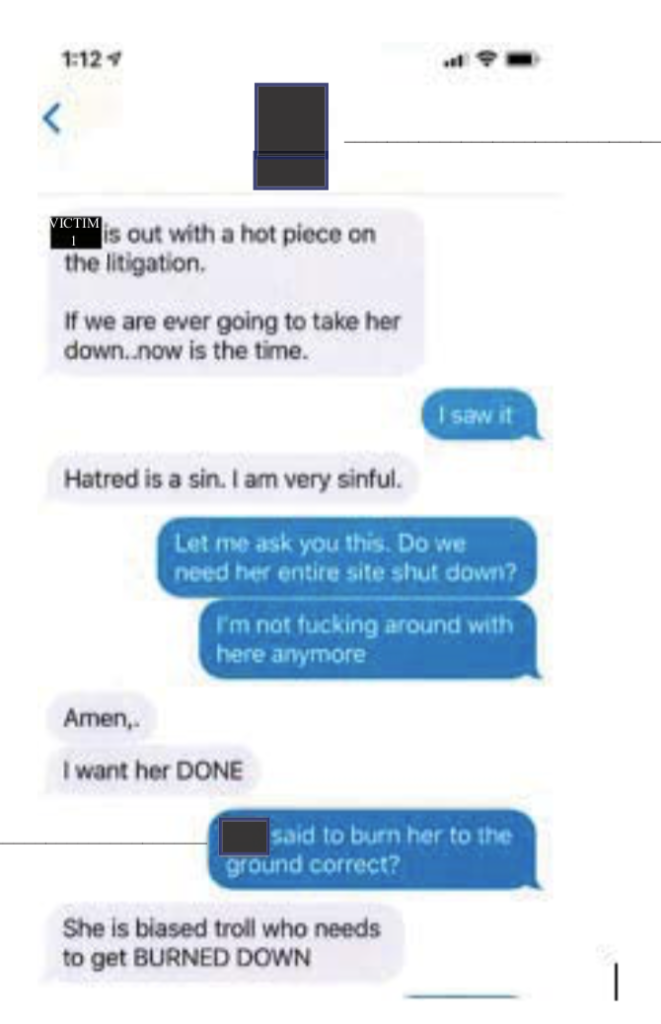
The scammers often pose as another young person, making contact on social media before moving to encrypted messaging apps and encouraging the victim to share intimate images.
They often make their blackmail demands within an hour of making contact and are motivated by extorting as much money as possible rather than sexual gratification, the NCA said.
pdh/bp
© Agence France-Presse